Urban Fantasist
Menu
|
URBAN FANTASIST |
0 Comments
HP up the ante in tech marketing with new Wolf cybersecurity ads series featuring Christian Slater15/2/2017 Here's a worrying video showing how easy it is to hack the new Furby Connect toy via a mobile phone app and its insecure Bluetooth protocol connectivity. But we love the idea of a shop full of Furbies chanting "We shall build a wall" and then launching into a Rickroll!
Here's the first of a new series of tech columns I'm writing...
|
Charles Christian was an English barrister, Reuters correspondent-turned editor, author, blogger, podcaster, award-winning tech journalist, storyteller, and sometime werewolf hunter, who sadly passed away in 2022.
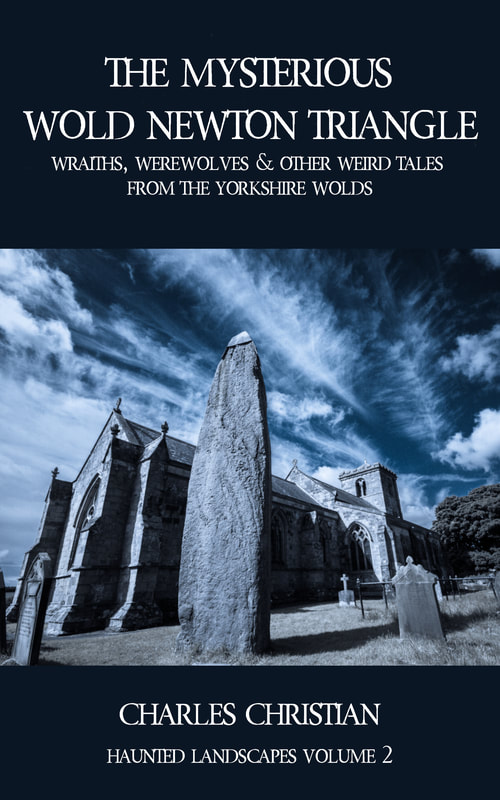
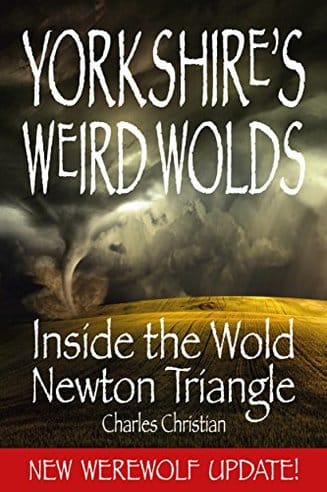
Prior to his sudden death he completed one of his largest works to date: The Witches Almanac, the definitive guide on the history of magic and folklore, including 359 of the most important witches and sorcerers in history. This site also has links to Charles' books and the Weird Tales Show videos and podcasts. Latest Video PostLatest book: The Wold Newton TriangleVirtual Tip JarYou can now support Urban Fantasist, its podcasts and its new video channel through our Virtual Tip Jars on PayPal and Patreon, giving you a choice of ad hoc or regular payments.
Contact DetailsEmail: urbanfantasist@icloud.com
Tel: +44(0)1986 788666 Tel/Txt: +44(0)7786 738172 WhatsApp etc: +44(0)7786 738172 Skype: ChristianUncut Twitter: @urbanfantasist Quote, Unquote"The only way to keep folklore alive is to share it" ...comment from viewer on YouTube channel
"Charles Christian... a man of paranormality" ...Howard Hughes, Talk Radio UK "Cynicism has always been a part of your (very impressive) brand" ...Kirk Fackre "Your storytelling set the scene for a fascinating evening of stunning music and terrifying drama" ...Chris Caswell "I can't help myself. Yesterday, I went back to this post over and over again and it made me laugh out loud each time. So now I'm bringing it to all my followers with the recommendation to follow Charles Christian because he posts lots of stuff that brightens my day and will brighten yours, too" ...LinkedIn commentator "A great witty intelligence in the world. We need more CC and less monkey-brained politicians" ...Julia Bohanna "I love your posts, always something interesting to read and often funny" ...Karen Morton "I was saddened to see you have retired your podcast. I never would have found your books without it. Well if a good story deserves rereading a good podcast demands relistening. Looking forward to your next stage with the time this change will afford you. Happy Trails, Pardner" ...Jonathan Neuhaus "You are a great and generous host" ...Patti Negri, The Hollywood Psychic "I host a daily morning show in Las Vegas and I like your shows very much. I love the way you pace your voice and thoughts is fantastic and you have a way of making your guest interviews sound more like conversations. Just wanted to let you know" ...Clay Baker "The ever wonderful Charles Christian and his Weird Tales Show"...Into The Portal Podcast "The Master of Mysteries & Folklore" ...Fantasy Radio UK "The witty and knowledgeable Charles Christian." "We poled our fans on their favorite podcasts and that's how I heard of Weird Tales Show. You are well loved by the geekiverse, and fans of folklore history and monsters!" "Charles Christian is really out there cool." "Charles Christian defiantly makes my world a brighter, funnier place." "The legendary Charles Christian at his eclectic best..." "Charles Christian is my inner spirit animal, thank you for making me laugh." "You always make me laugh! Thank you for brightening my day with your dark humour." "the funny, wonderful and slightly cantankerous Charles Christian" Charles Christian's Books |
|
Copyright © Charles Christian
& Urbanfantasist Limited 2022 |







 RSS Feed
RSS Feed